UnpacMe Weekly: Extractor Updates
This week we have added malware configuration extractors for Raccoon Stealer, and Redline Stealer.
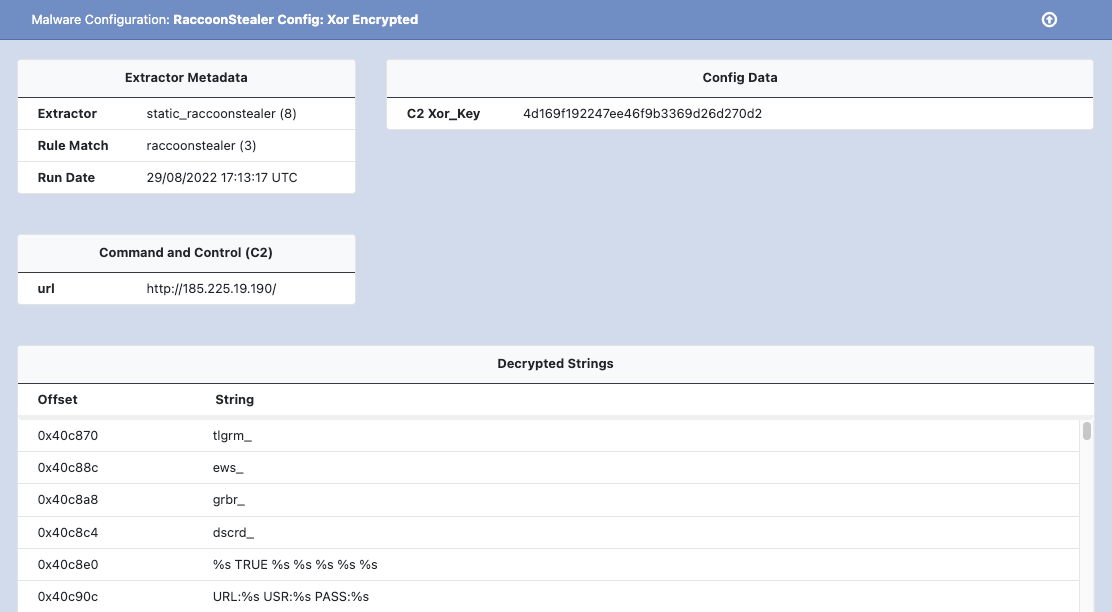
This week we have a few small malware config extractor updates we want to share. First, we've updated the RaccoonStealer extractor to support a new version of the malware that uses a unique key for each encrypted string. The previous version used a single key (ex: edinayarossiya) for all strings used by the malware. The malware has also changed from using RC4 to XOR for both C2 and string encryption.
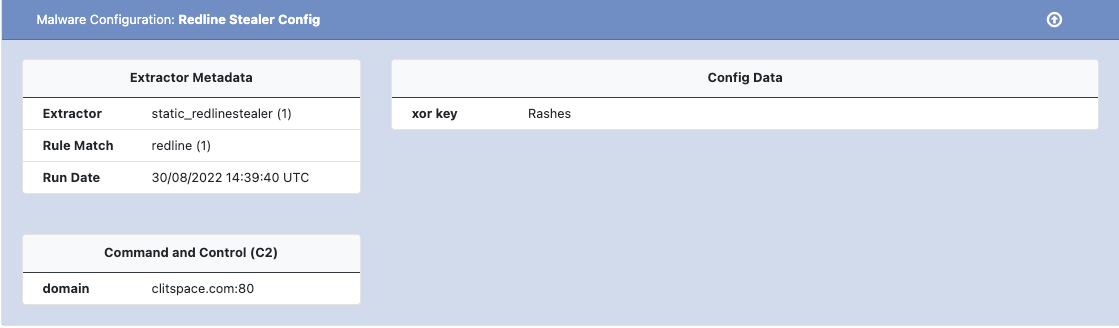
We have also added a new extractor for Redline Stealer - an information stealer written in .NET. Redline implements similar functionality as seen in other info stealers, such as: system fingerprinting, file grabbing, browser data, crypto wallets, and stealing various application credentials. As with other information stealers, Redline is often used by Access Brokers to obtain credentials from victims, which are then sold and used by other actors. An example of the Redline Stealer configuration can be seen below
As always, if you have any feedback or issues please let us know.
Happy Unpacking!